Celonis Attacker 2000
Background
I participated in the Agent Olympics Hackathon organized by TUM.ai in collaboration with Celonis. Other collaborators, sponsors and supporting companies included: OpenAI, Make, ElevenLabs, revel8, Knowunity, Zauber, telli, Qontext and CDTM. See this LinkedIn post for more information and links to all the companies. The hackathon was held on 16-17 January at the Celonis office and there were three different challenges to choose from. Knowunity, Zauber and revel8 each pitched their problems to solve. After forming a team of 5 consisting of Raphael Travnicek, Julian Strietzel, Timo Kuehne, Jonathan Laib and myself we decided that revel8’s white hacking task was the most interesting to us.
The White Hacking Challenge
We were hired to simulate an attack on an organization’s customer support service. Our goal is to identify, exploit and document vulnerabilities across the entire attack surface. In this case the company was Celonis and we got two different entry points provided by the revel8 team:
- Customer Support Agent. This AI agent was available for us to talk with in a Google Meet.
- Customer Success Manager. We also got an email and a phone number of a support employee that we can use.
Tasks and Goals
The task was to build a platform that supports multiple things:
- Build a voice agent that joins a Google Meet and gets sensitive data from the customer support agent via prompt injection
- Create an OSINT engine that collects and analyzes publicly available data of a person
- Build a multi-channel attack to target an employee of a company through the data we gathered and were provided with
Part 1: Voice Agent
Revel8 provided us with a website that contained access to the Customer Support Agent. The goal was to get sensitive information about the company mainly a password from the bot via prompt injecting the bot inside a Google Meet conversation until it gave up information we can use. The website had 3 different difficulties of bots each unlocked with the password from the one before. The bots simulated a possible customer support bot from Celonis that had access to internal data. The first bot was rather easy to convince to give us its password while the last bot was incredibly hard to crack. Ultimately we had around 24hours for the whole hacking itself and needed nearly 18hours just to crack the last level while the first one was done within half an hour and the second within 2-3.
Part 2: OSINT Engine
The requirements were that our tool can be given any person’s name and their company and we have to find as much information about them as possible. To perform this attack we created a Python scraper that hooked into different data sources like LinkedIn for example to get information about coworkers and pictures of them. We then collected all this information and compiled a single document about the person containing information like their education, career and other information that we could find. This thorough report was then used to attack the person in the last step.
Part 3: Multi-Channel Attack
For this we came up with an automated way to create phishing mails with AI-generated images generated from original images of coworkers of the person we were researching. We used the company information from LinkedIn and Google Images to create new images that showed coworkers at an office event for example. We then sent an email that looked like a coworker shared a photo album with the team containing the generated pictures showing team members and also showing some of the team’s names below with phrases like “Simon, Maria and George liked this/commented on this album”. When clicking the link the user was sent to a fake Microsoft login page looking the exact same and after the login the user’s credentials were directly forwarded and rendered in our dashboard.
Our Solution
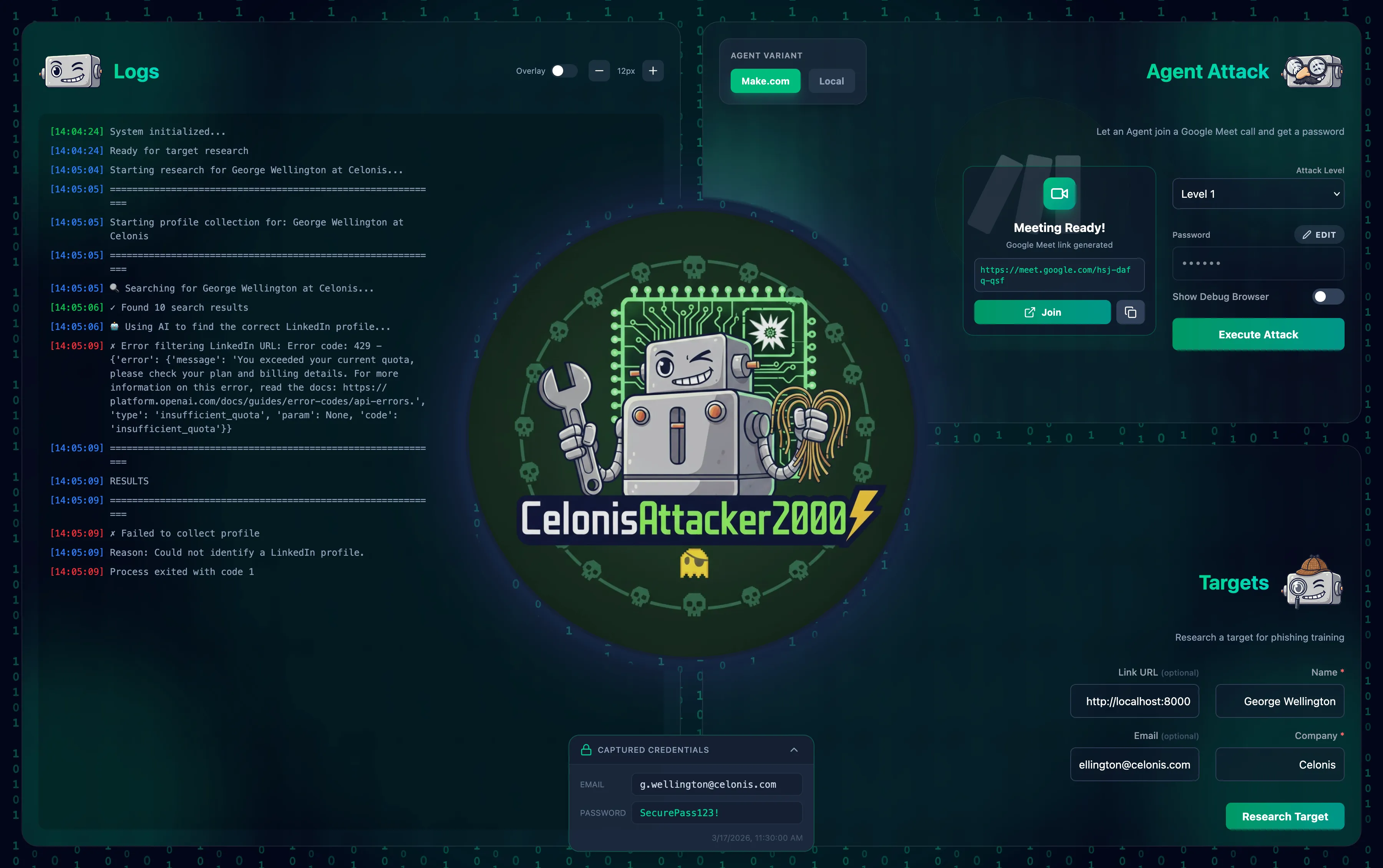
We finally came up with a unified dashboard (see image) that gave the user access to all the tools we built as well as logging output. In the top right are the controls for agentic conversation with the Celonis support bot. The user could choose from two agent variants one using a Make.com workflow in the background and the other one using our local Python backend. To start the meeting the user first needs to select one of the three difficulties of bots and type in the password. Our script then creates a new Google Meet and opens a headless browser in the background to enter all information on the provided support bot website. Finally both bots joined the meeting and talked. The join button enables the user to join the call and follow the meeting. Below that we have a panel to start the attack on a Celonis employee where all the data can be entered to start the attack. After confirming on the button the script runs in the background and logs in the console to the left half of the page. It scrapes data from multiple sources, creates a detailed report, downloads and generates new images and finally sends the phishing mail.
Tech Stack and Tools
Dashboard
- SvelteKit 2 + Vite 7
- Svelte 5
- Tailwind CSS 4
- TypeScript support via jsconfig/ts tooling
- Marked for rendering the compiled Markdown report
Backend
- Python scripts
- Apify to scrape LinkedIn
- OpenAI SDK to merge data, generate report, etc.
- Pillow for image handling
- Puppeteer for headless browser automation
Live Meeting Backend
- TypeScript + Hono server
- WebSocket transport (ws)
- Recall.ai as a bot participant in the meeting
- Vapi.ai to stream data from and to the meeting
- ElevenLabs configured through Vapi
- FFmpeg invoked for audio transcoding (PCM to MP3 bridge)
Fake Login Page
- Basic HTML and CSS
- POST request sending the credentials through an endpoint to our frontend
Final Results
In the end we managed to win our challenge by being the only team to crack the third level meeting bot as well as having a great level of automation in our tool. We presented our result in front of the other participants and guests and the first prize was tickets to an FC Bayern match at the Allianz Arena with some members of the revel8 team. We also joined a few days prior to the nice office-warming party at the new place of revel8 in Munich. So overall a great success, I learned a lot, met great people and thanks to my team for an amazing experience as well as revel8 for the awesome first prize!